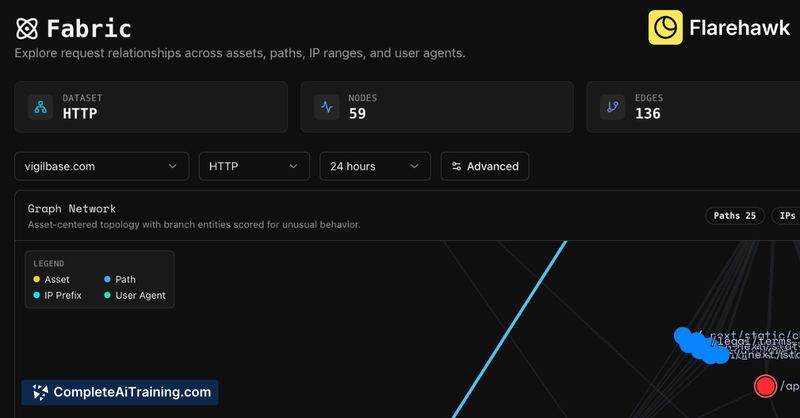
About Flarehawk
Flarehawk is a security monitoring tool that performs real-time threat detection, automated investigation, and one-click remediation based on your environment's own behavior. It builds a per-tenant machine learning model from ingested logs, retains logs for five years, and includes single sign-on and team messaging integrations out of the box.
Review
Flarehawk is focused on reducing alert noise and accelerating incident response by scoring anomalies against an environment-specific baseline rather than a generic threshold. At launch it supports enterprise log exports and is available in open beta with a short trial period, so expect active feature rollouts and periodic updates.
Key Features
- Per-tenant ML model that learns each environment's baseline and scores anomalies accordingly.
- Real-time detection with automated investigation workflows and one-click fixes for common remediations.
- Full log ingestion without sampling and five-year log retention for historical analysis and audits.
- Built-in SSO and integrations with team messaging platforms for alerting and collaboration.
- Short model warm-up (minutes to an hour depending on traffic) and ongoing model refinement.
Pricing and Value
Flarehawk launches in open beta and offers a one-month free trial; paid usage is required after the trial. Early availability is focused on enterprise log export paths, with additional ingestion connectors planned. The main value comes from reduced alert fatigue and faster remediation workflows driven by environment-specific models and automated investigations. Organizations that can stream full logs into the platform will see the most benefit, while teams with limited log sources should evaluate integration timelines before committing.
Pros
- Environment-specific ML reduces generic false positives and helps prioritize meaningful alerts.
- Automated investigation plus one-click remediation speeds up response and rollback testing.
- Long retention window (five years) supports compliance and historical forensics.
- Built-in SSO and team messaging integration streamline operations and notification routing.
- Short initial warm-up means useful insights appear quickly after onboarding.
Cons
- Initial support is limited to specific enterprise log export methods; broader connector support is still being added.
- Currently focused on log ingestion and analytics; metrics-style monitoring and custom dashboards are on the roadmap but not fully available yet.
- As an open beta product, expect occasional rough edges and active changes to features and pricing.
Flarehawk is best suited for security teams and infrastructure owners who receive large volumes of alerts and can provide continuous log streams from their infrastructure. It fits organizations that need faster triage and remediation and are comfortable adopting an open beta service while additional integrations and dashboarding capabilities arrive.
Open 'Flarehawk' Website
Your membership also unlocks: